Do these sound familiar?
Backlog overload
“We can’t tell which findings actually matter”
- >Real risk not surfaced
- >Severity scores without context
- >No proof of exploitability
Resource misallocation
“Our exposure grows faster than our fix capacity”
- >Longer exposure windows
- >Higher breach likelihood
- >Missed SLAs
No rip and replace
“We waste 20% of dev time without reducing risk”
- >Lost engineering capacity
- >Tickets ping-pong
- >Slipping roadmap
You don’t need more findings.
You need context-aware triage.
Because without context, triage is guesswork.
With it, you get proof & ship faster with less risk.
Built for your entire AppSec stack
Konvu triages findings across your entire application security stack, with evidence for every decision.
Software Composition Analysis
SCA Triage
Auto-dismiss non-exploitable dependency vulnerabilities with evidence. Cut through the 85%+ of SCA findings that don't pose real risk.
Static Analysis
SAST Triage
Confirm which static analysis findings are actually reachable and exploitable in your codebase.
Remediation
Auto-Fix
Automated, safe remediation with evidence that the fix resolves the actual risk. PRs with context, not blind upgrades.
Coming soonContainers
Container Triage
Identify which container dependencies are actually used and exploitable.
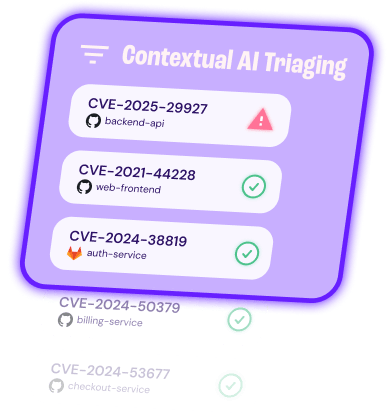
Cut through the noise with evidence-backed triage
AI agents verify exploitability with deterministic checks, then write decisions and evidence back into your tools. Auto-dismiss what is not exploitable. Escalate what is. Keep a reviewable audit trail.
Auto-dismiss with an audit trail
Dismiss non-exploitable vulnerabilities with decisions backed by reasoned analysis and evidence your security and dev teams can trust.
- Cut backlog and noise by ignoring non-exploitable findings with confidence.
- Trust every decision with documented investigations, code-level and optional runtime evidence.
- Stay in control with policy-based confidence thresholds and human-in-the-loop reviews.
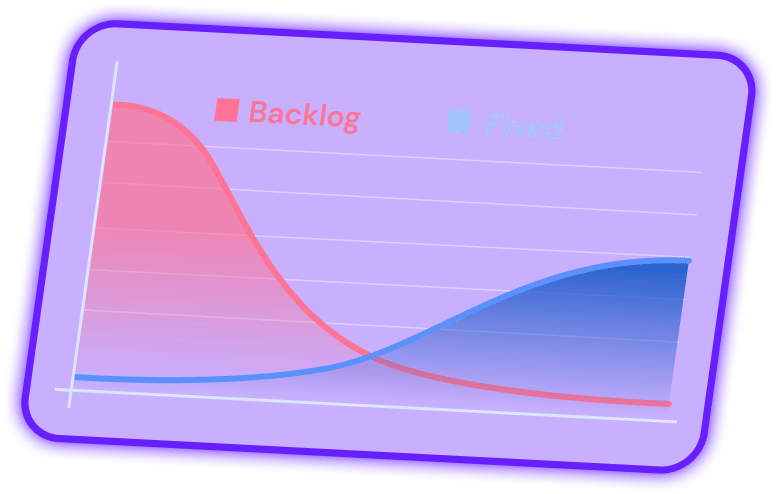
Zero in on exploitable vulnerabilities
Surface the few vulnerabilities that are actually exploitable so teams act fast and meet SLAs.
- Check exploit conditions against Konvu's vulnerability database enriched with exploitability conditions and affected functions.
- Confirm exploitability with evidence beyond reachability by running deterministic checks on code paths, configs, data flows and optional runtime signals.
- Prioritize vulnerabilities based on business context, Known Exploited Vulnerability (KEV), or Exploit Prediction Scoring System (EPSS).
Built for your workflow
Keep your scanners and process. Konvu installs quickly and pushes decisions where work already happens.
- Install in minutes with lightweight setup that supports your languages and technologies.
- Keep your scanners and avoid rip-and-replace or partial coverage from a new tool.
- No new dashboards: decisions sync into your tools so teams keep their process.
Average noise reduction
Fortune 500 Retail
Security Lead
Konvu gave us clarity. It dismissed the non exploitable findings and put the real risks at the top of the list.
Faster MTTR on real issues
Fintech SaaS
CISO
“We went from drowning in Snyk alerts to having a clear, prioritized view of what actually matters.”
Learn how a retail giant with 80k+ employees transformed their vulnerability management by automatically triaging Black Duck Polaris findings with AI-powered evidence.
Read case study →